
Swiss intelligence benefited from CIA-Crypto spying affair
A Swiss parliamentary investigation has revealed that Swiss intelligence service were aware of and benefited from the Zug-based firm Crypto AG’s involvement in US-led spying.
According to the conclusions of a nine-month investigationExternal link by the Swiss parliamentary audit committee, published on Tuesday, the Swiss intelligence service knew that the US Central Intelligence Agency was behind the Swiss-based Crypto AG as far back as 1993. The report says that Swiss intelligence later collaborated with them to gather information from foreign sources.
The audit committee investigation was prompted by revelations in February by Swiss public television SRF, German television ZDF and the Washington Post that Crypto was at the heart of a huge international spying operation led by the CIA, but also involving the German BND spy service.
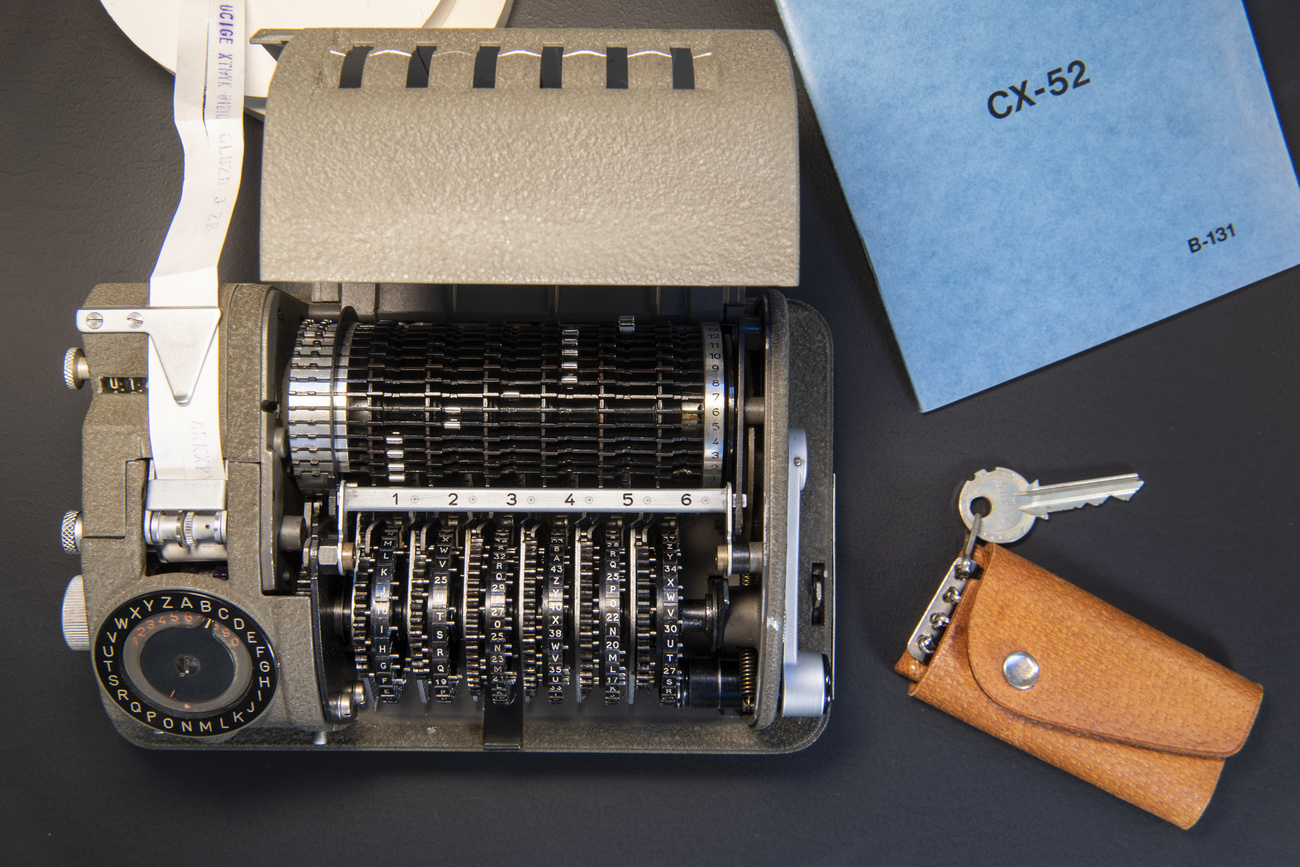
More than 100 countries bought the encryption devices from the Zug-based company, which did business under the guise of Swiss neutrality. In reality, the firm belonged to the CIA and Germany intelligence service, which could freely read what it encrypted. Information intercepted with the help of Crypto’s devices changed the course of events including the Iran hostage situation in 1979.
Crypto never delivered encrypted devices to the Swiss authorities. However, Switzerland has taken advantage of the eavesdropping made possible by these devices according to the report. This was a service to our country said Philippe Bauer, a member of the parliamentary delegation leading the investigation. This was especially the case for the hostage affair in Libya.
The investigation sought to determine who in the Swiss government knew about the affair and when. As part of the investigation, the committee examined how, given the political significance, the Swiss intelligence service and foreign intelligence services were able to jointly use a company located in Switzerland without parliament’s knowledge.
“The fact that this collaboration could have been concealed from the Federal Council for so long also highlights shortcomings in the management and supervision exercised by the latter,” the report states. With this, it says that the highest office in Switzerland shares some responsibility for Crypto’s activities.
The current government ministers were only informed of the affair in autumn 2019, a few months before SRF published its report.
Swiss politicians reacted to the investigation findings, many calling for further steps to be taken to understand the full extent of the relationship between Swiss intelligence and Crypto’s services with the CIA. “This banana republic behaviour is unworthy of a constitutional state and must have political and personnel consequences,” said Balthasar Glättli, from the Green Party. Of particular concern is the fact that people in the Swiss defence ministry destroyed files between 2011 and 2014.
The audit delegation makes twelve recommendations to the government. They range from the conditions for informing the authorities quickly in such cases to the acquisition of encryption tools by the armed forces and the archiving of intelligence documents.
Export ban
The report also criticises the decision by the State Secretariat of Economic Affairs to revoke Crypto International’s export license. Crypto AG was taken over by Crypto International, a Swedish-owned cybersecurity company based in Zug, that is said to have no ties to foreign intelligence services. Due to the ban, the Swedish company had to scale back activities in Switzerland.
The Swiss attorney general initiated criminal proceedings against Crypto International in June over alleged false or incomplete information that had been provided to SECO in its export applications. SECO, the authority responsible among other things for the licensing of war materiel exports, believes it was misled by the Zug-based company when it filed export applications for its devices.
The parliamentary audit committee found that there was no legal grounding for the criminal complaint. The committee recommends that the government re-examine the suspended export licenses and that the criminal complaint be withdrawn.

In compliance with the JTI standards
More: SWI swissinfo.ch certified by the Journalism Trust Initiative

























You can find an overview of ongoing debates with our journalists here . Please join us!
If you want to start a conversation about a topic raised in this article or want to report factual errors, email us at english@swissinfo.ch.